MafiaWare666 is a ransomware that will take over your computer functionality and lock your computer (.MafiaWare666 extension) until you pay a “ransom” in order to decrypt your files and get access back. The ransom is in the form of Bitcoin for USD $300/EUR €300 to be settled within 72 hours. It disguises itself as a legit official warning when in reality it is all fake. Don’t fall for the trap and don’t pay any ransom fees! With software, you can remove the MafiaWare666 ransomware easily. This type of infection can be downloaded on your computer for many reasons such as malicious websites, codecs, or downloads. Be sure to remove it immediately.
Category: Ransomware
How to Remove the ZXCVB Ransomware
ZXCVB, belonging to the Dharma family, is a ransomware that will take over your computer functionality and lock your computer until you pay a “ransom” in order to get access back. It encrypts one’s computer files and appends the victim’s ID plus the .[paymoney@onionmail.org].zxcvb extension to file names. This ransomware disguises itself as a legit official warning when in reality it is all fake. Don’t fall for the trap and don’t pay any ransom fees in Bitcoin. With software, you can remove the Zxcvb ransomware easily. This type of infection can be downloaded on your computer for many reasons such as malicious websites, codecs, or downloads. Be sure to remove it immediately.
How to Remove Ooxa (.ooxa) Ransomware
Ooxa is a ransomware that will take over your computer functionality and lock your computer until you pay a “ransom” in order to get access back. It disguises itself as a legit official warning when in reality it is all fake. This ransomware, a STOP/DJVU variant, will add an .ooxa extension to all files making it unaccessible unless you make a payment in Bitcoin.
Don’t fall for the trap and don’t pay any ransom fees. With software you can remove the Ooxa ransomware easily. This type of infection can be downloaded on your computer for many reasons such as malicious websites, codecs, or downloads. Be sure to remove it immediately.
How to Remove GetAnAntivirus Ransomware
Belonging to the Chaos family, GetAnAntivirus is another ransomware that will take over your computer functionality and lock your computer until you pay a “ransom” in order to get access back. It leaves a read_it.txt file as ransom note which reads:
Hi I´m Your Mum,
Ok no, I’m actually a Virus and Your PC is now mine. (btw I encrypted all your files)
Don’t worry, you can get them back.
How can you get them back?
Well,…
You must follow these steps To decrypt your files :
1) Write on our e-mail: AnnaSenpai947603@proton.me.
2) Get some Bitcoins, because to get your files back, you have to pay 500$ to my Wallet.
(by the way it’s 19DpJAWr6NCVT2oAnWieozQPsRK7Bj83r4)
3) Send us a proof, that you sent the money. (Screenshot, etc.)
Pro tip:
Get a good Antivirus (My Choise: MalwareBytes)
The note disguises itself as a legit official warning when in reality it is all fake. Don’t fall for the trap and don’t pay any ransom fees. With software, you can remove the GetAnAntivirus ransomware easily. This type of infection can be downloaded on your computer for many reasons such as malicious websites, codecs, or downloads. Be sure to remove it immediately.
How to Remove HKGT (.hkgt) Ransomware
HKGT is a ransomware from the STOP/DJVU family that will take over your computer functionality and lock your computer until you pay a “ransom” in order to get access back. What it does is encrypt all user files with the .hkgt extension and leaves a _readme.txt file which contains contact details and payment info. It disguises itself as a legit official warning when in reality it is all fake. Don’t fall for the trap and don’t pay any ransom fees. With software, you can remove the HKGT ransomware easily.
This type of infection can be downloaded on your computer for many reasons such as malicious websites, codecs, or downloads. Be sure to remove it immediately.
How to Remove the TRINS Ransomware
TRINS is a ransomware that will take over your computer functionality appending your files with the .trins extension. It will lock your computer making you lose access to files until you pay a “ransom” (via bitcoin) in order to get them back. It disguises itself as a legit official warning when in reality it is all fake. Don’t fall for the trap and don’t pay any ransom fees! With software, you can remove the TRINS ransomware easily. This type of infection can be downloaded on your computer for many reasons such as malicious websites, codecs, or downloads. Be sure to remove it immediately.
How to Remove the GTYS Ransomware
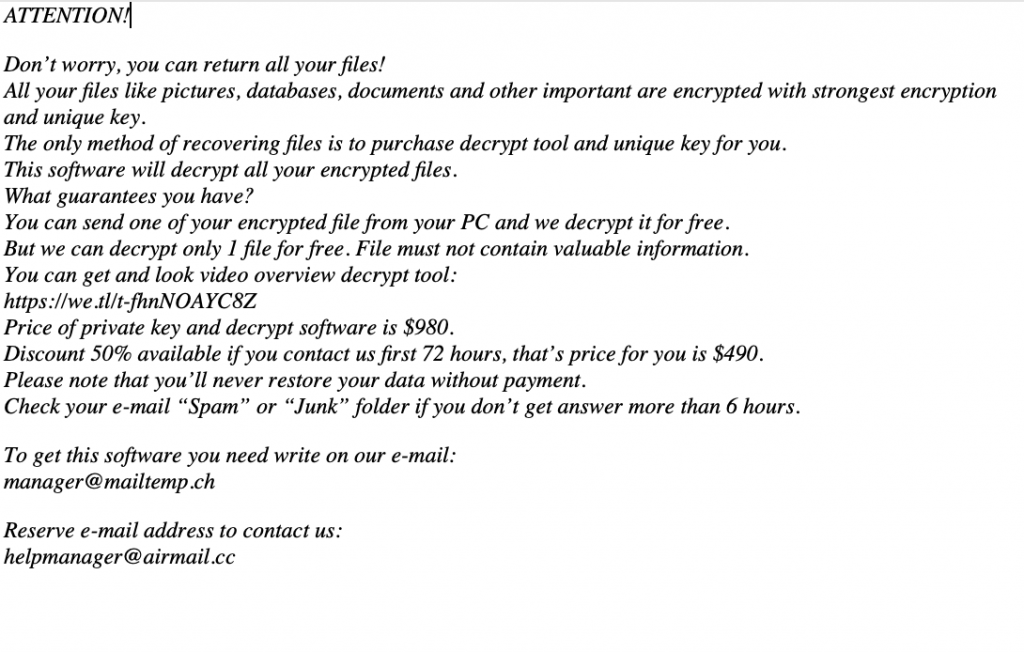
GTYS, from the STOP/DJVU family, is a file-encrypting ransomware that will take over your computer functionality and lock your computer until you pay a “ransom” in order to get access back. It appends user files with the .gtys extension and displays a _readme.txt file for instructions how to decrypt the data.
ATTENTION!
Don’t worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-xxxxxxxx
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
To get this software you need write on our e-mail:
support@sysmail.ch
Reserve e-mail address to contact us:
supportsys@airmail.cc
Your personal ID:
XXXXXXXXXXXXXX
It may look as a legit official warning when in reality it is all fake. Don’t fall for the trap and don’t pay any ransom fee of $980. With software, you can remove the GTYS ransomware easily. This type of infection can be downloaded on your computer for many reasons such as malicious websites, codecs, or downloads. Be sure to remove it immediately.
How to Remove Loov Ransomware
Loov is a ransomware belonging to the STOP/Djvu family that will take over your computer functionality and lock your computer until you pay a “ransom” in order to get access back. What it does is encrypt your files and append them with the .loov extension.
A ransom note (_readme.txt file) will disguise itself as a legit official warning when in reality it is all fake.
Don’t fall for the trap and don’t pay any ransom fees. With software, you can remove the loov ransomware easily. This type of infection can be downloaded on your computer for many reasons such as malicious websites, codecs, or downloads. Be sure to remove it immediately.
How to Remove the Psychopath Ransomware
Psychopath is a ransomware that will take over your computer functionality and lock your files until you pay a “ransom”, in the form of Bitcoin cryptocurrency, in order to get access back. What it does is modify the file names with a unique string ID assigned to the victim. It then appends – [psychopat7@tutanota.com].[4-character string file extension] to each file. The ransom note from the Read_Me!_.txt file reads:
Your Data Locked.
To Get Decryption Instructions Email Us ,Don’t Edit Files Or Folders !
ID : xxxx
Email Address :psychopath7@tutanota.com
It disguises itself as a legit official warning when in reality it is all fake. Don’t fall for the trap and don’t pay any ransom fees. With software, you can remove the Psychopath ransomware easily. This type of infection can be downloaded on your computer for many reasons such as malicious websites, codecs, or downloads. Be sure to remove it immediately.
How to Remove Zoom Ransomware
Zoom ransomware will take over your computer functionality and encrypt your files until you pay a “ransom” in order to get access back. It disguises itself as a legit official warning when in reality it is all fake.
YOUR COMPUTER HAS BEEN HACKED
ATTENTION!
YOUR IMPORTANTFILES VS YOUR MONEY
Don’t worry, you can return all your files!All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.The only method of recovering files is to purchase decrypt tool and unique key for you.This software will decrypt all your encrypted files.
- YOU FIRST CONTACT OUR TEAM IN MAIL ADDRESS:-ransomware10@yahoo.com
OUR SOFTWARE PRICE ONLY 10$ PAYMENT AVILABLE ONLY BITCOINS
BITCOIN WALLET ADDRESS:-17CqMQFeuB3NTzJ2X28tfRmWaPyPQgvoHV
NOTE:- YOU MUST BUY
OUR TOOL WITHIN 7
DAYS IF YOU DON’T
BUY OUR TOOL WE
WILL DELETE YOUR ALL
FILES PERMENENELY
Don’t fall for the trap and don’t pay any ransom fees! With software, you can remove the Zoom ransomware easily. This type of infection can be downloaded on your computer for many reasons such as malicious websites, codecs, or downloads. Be sure to remove it immediately.